PHI Protection in Transit and at Rest: Practical EDI Security Patterns for Health Insurers


Health insurance payers have spent years fine-tuning their EDI systems for compliance and operational efficiency, but major hidden costs and risks still lurk in many EDI workflows. Far from being just a compliance checkbox, PHI protection in transit and at rest is critically tied to underlying EDI patterns, especially when legacy manual processes and overlooked technical debt drive up risk and cost.
Why Spreadsheet-Based EDI Monitoring Costs Health Plans More Than They Realize
If your team leans on spreadsheets or manual lists to track EDI file movement, exceptions, or enrollment changes, you’re likely absorbing costs that rarely appear on a balance sheet. Manual EDI monitoring almost always grows out of necessity—teams patch together Excel trackers or scripts when faced with limited EDI system visibility—but these workarounds present real PHI risks and operational drag:
- Blind Spots for PHI Events: Spreadsheets rarely update in real time, so you may miss or delay detection of unauthorized file transfers, missing inbound enrollments, or subtle data loss events. Even a short lag risks PHI exposure or compliance failures.
- Security Gaps: Locally stored spreadsheets might not be encrypted, leaving historical claims or eligibility data unnecessarily exposed. There’s no access control, no audit trail, and certainly no automated anomaly tracking for suspicious changes.
- Scaling Risks: As volume and complexity grow, manual logs simply can’t track every EDI file or interaction. Missed events become the rule, not the exception.
Ultimately, these hidden costs go far beyond inefficiency. PHI risk, IT burnout, and SLA penalties can cascade from manual tracking alone. Want a deeper dive into how these seemingly small inefficiencies quietly drive up costs?
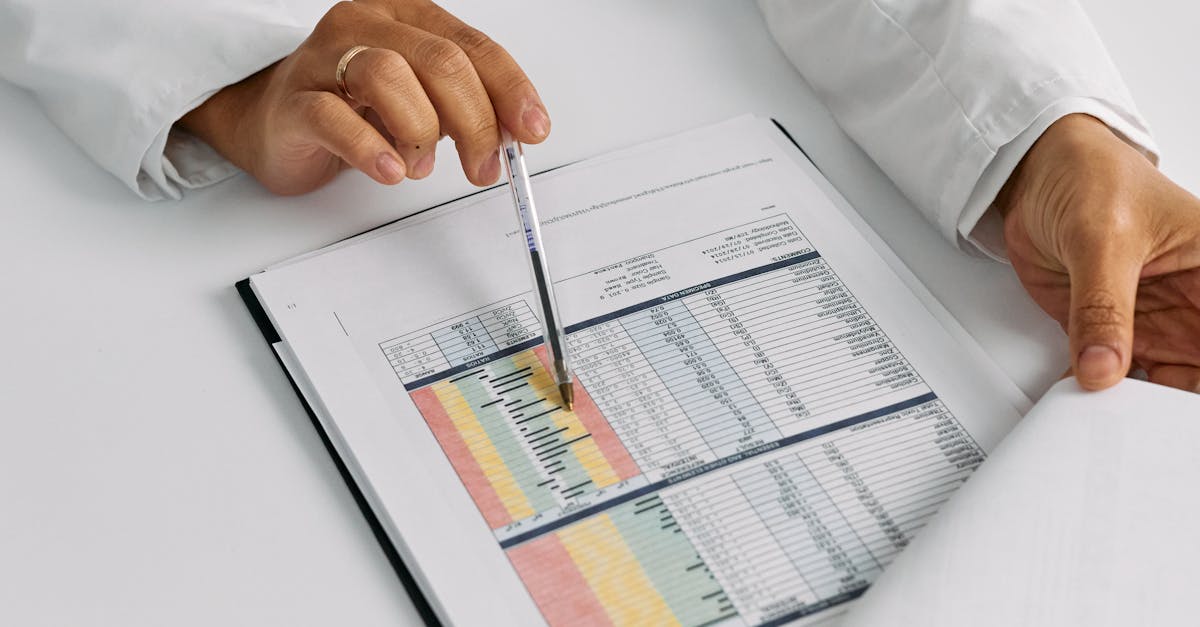
The Hidden Cost of SLA Penalties in Health Insurance EDI
Whenever manual oversight lets a file slip or a PHI-related error go undetected, SLA violations and penalty clauses can come into play. Most trading partner agreements enforce turnaround time, file acknowledgment, data integrity rules, and even notification requirements for PHI exposure. The hidden costs include:
- Direct Financial Penalties: Even a single missed file or late 834/837 can lead to thousands in fines per event, and recurring misses compound monthly.
- Remediation and Investigation Hours: Teams scramble reactively, spending high-value IT and compliance hours retracing steps to document what happened, and what wasn’t tracked in the spreadsheet.
- Future Revenue Impact: Trading partners facing repeated SLA issues may renegotiate pricing, demand new terms, or ultimately seek partners with stronger operational guarantees.
It’s not uncommon to see organizations invest heavily in front-end EDI mapping but underinvest in real-time file tracking, audit trails, or automated alerts. This disconnect only becomes visible after a costly event. For a look at how modern dashboards and real-time monitoring can help, check out our post on upgrading from spreadsheets to dashboards.
Manual EDI Exception Handling: The #1 Resource Drain on IT Teams
Manual exception tracking—such as using emails, ticket queues, or Excel logs to resolve missing files or data mismatches—can be both a security risk and a massive drain on IT and operations. Typical hidden resource costs include:
- Excessive IT Touches: Each exception can generate dozens of emails, file pull requests, and manual lookups for PHI-containing records. This keeps teams away from higher-value automation or analytics work.
- Opaque PHI Workflows: Lacking integrated audit trails, no one can easily prove who touched PHI, when exceptions were resolved, or if corrections exposed data further.
- Compliance Bottlenecks: Generating HIPAA-mandated incident or breach reports is painful when documentation is scattered and incomplete. This can slow audits, increase legal risk, or drive up stress come reporting season.
Eliminating manual exception resolution closes both a cost and compliance gap.

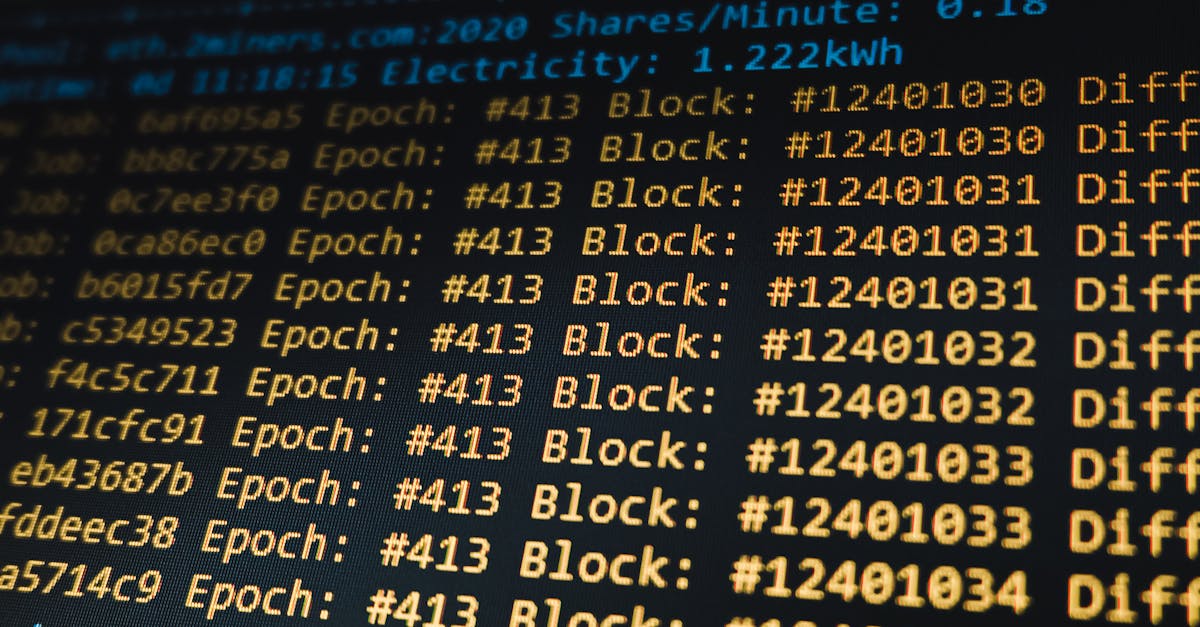
Missed Files, Missed Revenue: How Aging Pages Prevent Hidden EDI Failures
In health insurance EDI, a missing 834 or 837 file isn’t just a delay. It can prevent enrollments from activating, claims from being paid, or in worst cases, expose PHI due to manual workarounds or poorly secured retransmissions.
- Aging Pages as Risk Multipliers: Many legacy EDI dashboards or portals present “aging pages” that show only surface-level status, failing to alert admins to files missed entirely or silently aging in SFTP folders. PHI risk grows the longer files sit undetected.
- Downstream Revenue Loss: For each missed eligibility file, downstream premium processing stalls. For claims files, provider and member satisfaction suffers and revenue recognition slows. These losses are often hidden in operational budgets, only surfacing during end-of-year reviews.
- Hidden Security Breaches: Unmonitored or unreconciled files can lead staff to transmit PHI outside formal workflows (for example, email or non-secured channels), compounding exposure risk.
The cure is holistic, real-time EDI visibility: tracking every file from arrival to completion, with audit trails showing every PHI touch point. For practical strategies to go beyond surface-level monitoring, visit our guide to solving EDI pain points.
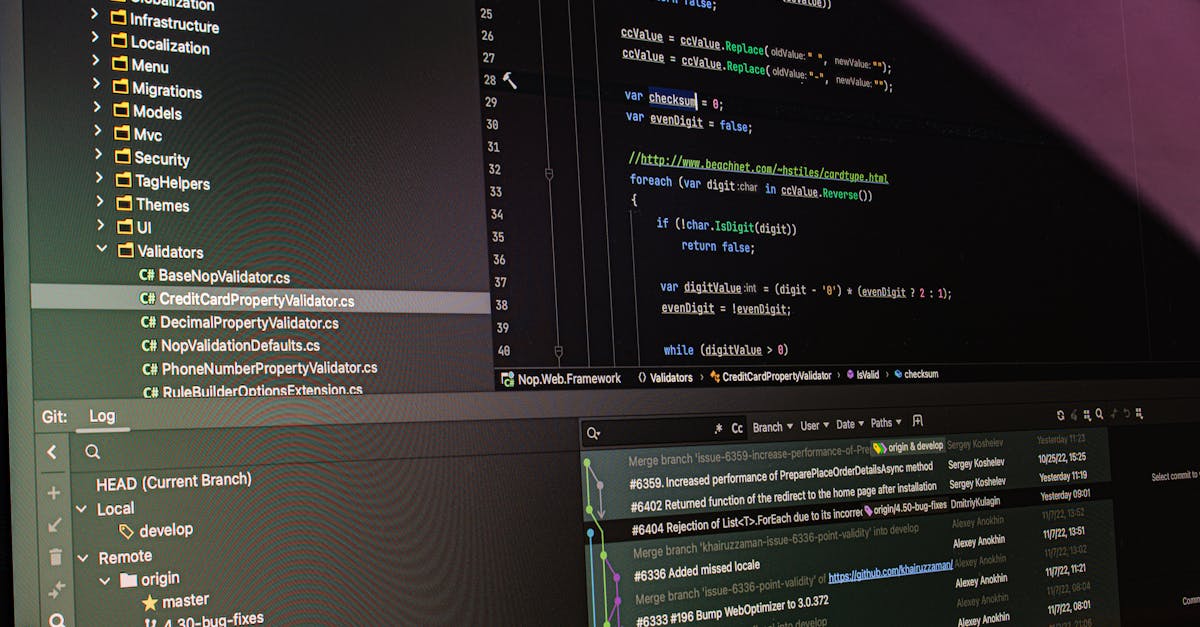
Key EDI Security Patterns for Robust PHI Protection
To move away from hidden costs, compliance risk, and revenue leakage, payers must adopt EDI patterns that actively protect PHI throughout its lifecycle:
- End-to-End Encryption: Use strong encryption by default—TLS 1.3, SFTP, and AES-256—across every interface, from file handoffs to internal storage. Don’t rely on partner assurances alone; verify encryption everywhere PHI moves or rests.
- Real-Time Audit Trails: Every file touch—upload, download, correction, exception—should be logged and searchable for at least HIPAA’s required period. Automated trails mean you’re never scrambling to reconstruct incidents or prove compliance.
- Granular Role-Based Access (RBAC): Lock down file and PHI access by user role, not just by IT group. Enable MFA and review access at regular intervals, not just yearly audits.
- Automated Alerts and Monitoring: Proactive systems catch missing files, delayed transmissions, or unauthorized access instantly.
- Integrated Exception Handling: Embed resolution and reconciliation directly into your EDI workflow, not as afterthoughts managed in tickets or email. Real-time clearing of issues keeps PHI exposure windows to a minimum.
These patterns aren’t just technical best practices; they’re business safeguards. Our team at EDI Sumo specializes in automating and enforcing these controls so payers can move beyond outdated, manual processes and hidden risks.

What Health Insurers Gain by Modernizing PHI Security
- Reduced SLA Penalties: No more excusing missed files or slow acknowledgments to partners. Proactive alerting and audit trails back up compliance claims and keep trading partners satisfied.
- Less IT Burnout: Automation frees IT from draining exception research, manual file pulls, or scrambling when auditors knock. Teams spend more time on strategic projects, less on firefighting.
- Greater Revenue Assurance: Continuous, end-to-end EDI monitoring keeps cash flow predictable, reduces member enrollment backlogs, and helps ensure claims are clean and timely.
- Harder Security Posture: With encryption, RBAC, and immutable audit logs, PHI risks fall rapidly even as complexity and file formats grow.
When PHI security is woven directly into your EDI workflow, hidden costs, risks, and obstacles melt away.
Get Ahead of the Risks: Make the Shift from Manual to Modern
If you’re ready to see what transparent, real-time PHI protection looks like in practice—or if you’re tired of battling hidden costs and resource drains in your EDI processes—we invite you to connect with EDI Sumo for a conversation. Our mission is helping payers see and solve the practical security and workflow gaps that cost more than they realize, so you can focus on member satisfaction, compliance, and true business resilience.


.png)



.png)

.png)


.png)
